Router Kali Linux Internet Proxy server Wireshark, linux, computer Network, electronics, text png | PNGWing

kali linux Proxy " T-shirt for Sale by Risala | Redbubble | kali linux t-shirts - proxy t-shirts - anonymous t-shirts

Error “E: Unable to locate package dnscrypt-proxy” in Kali Linux and Debian (SOLVED) - Ethical hacking and penetration testing

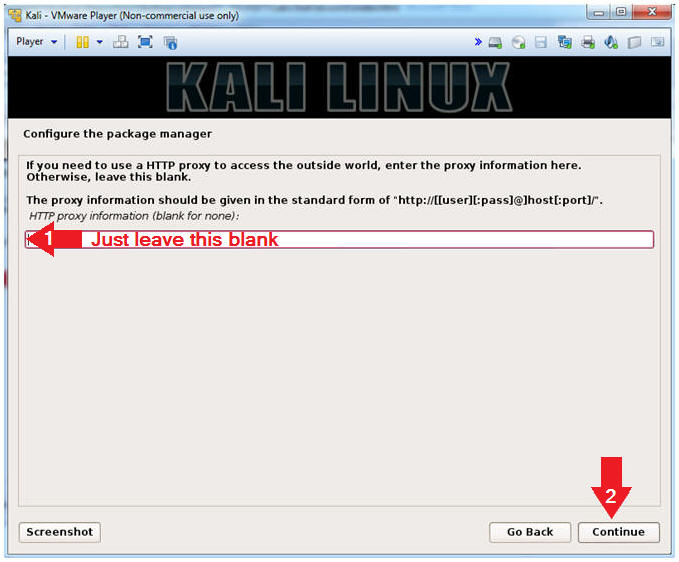
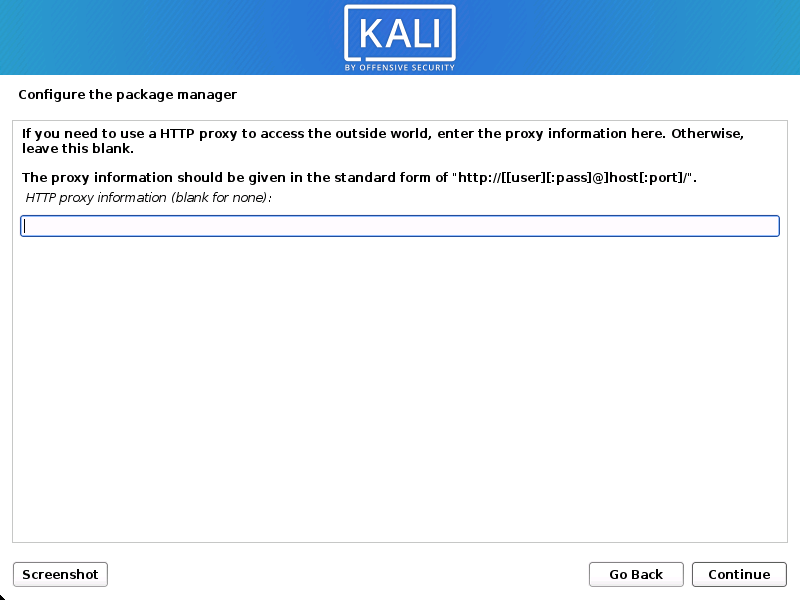
Creating a redirect proxy on Windows for Kali Linux attacking VMs (VMWare) – ListerUnlimited.com & DarkInternetMotherfuckers.com

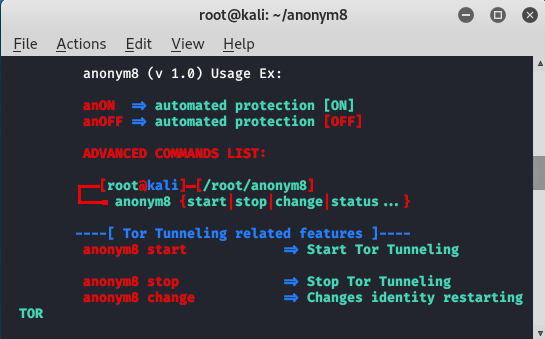
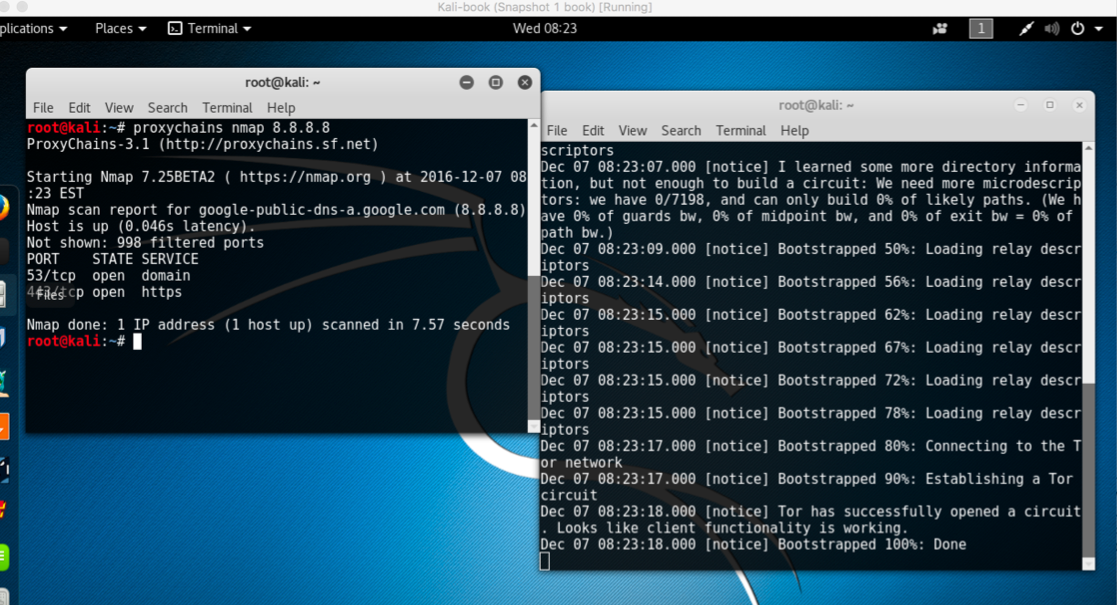
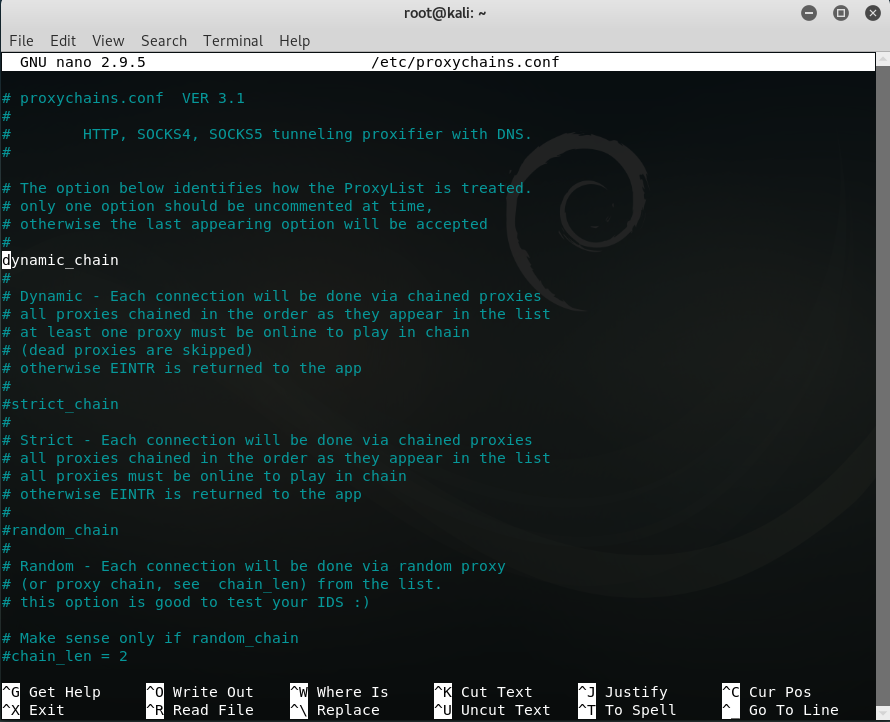
Configuring programs and operating systems to work through a proxy - Ethical hacking and penetration testing
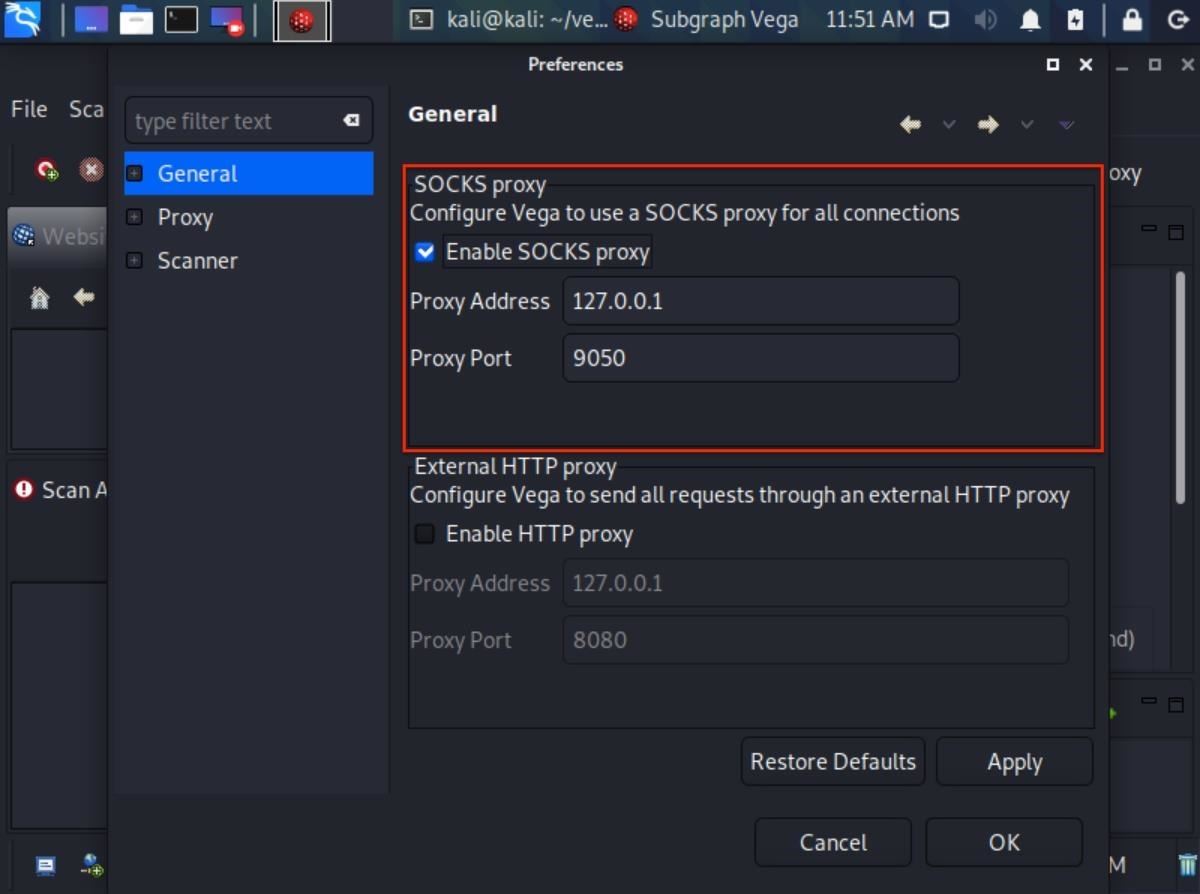
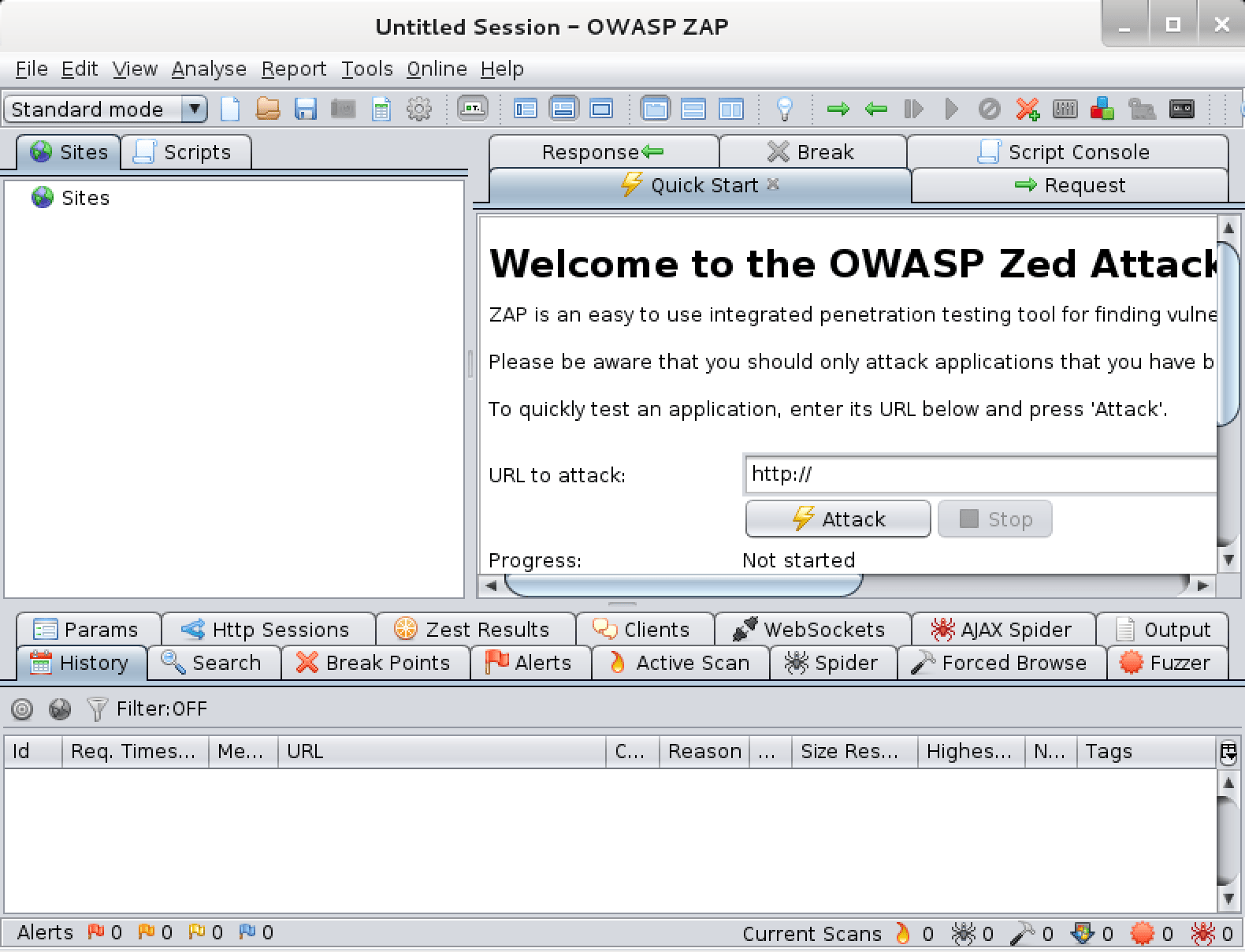
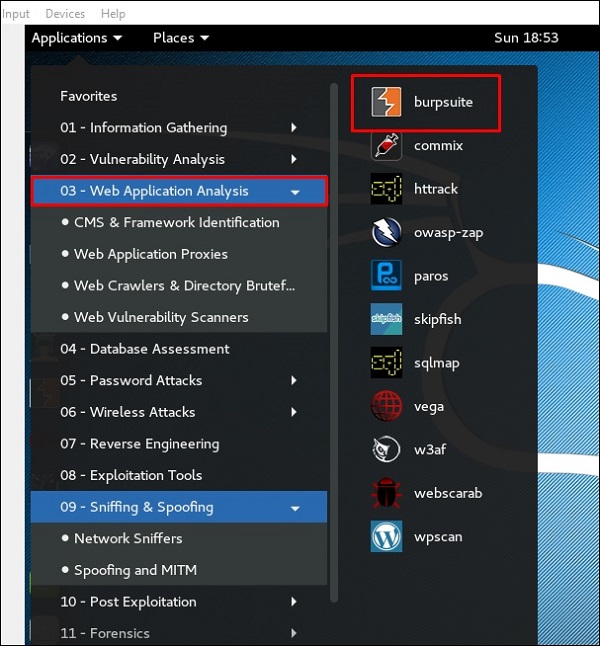
How to Scan Websites for Potential Vulnerabilities Using the Vega Vulnerability Scanner in Kali Linux « Null Byte :: WonderHowTo
![Adjusting network proxy settings - Mastering Kali Linux for Advanced Penetration Testing - Third Edition [Book] Adjusting network proxy settings - Mastering Kali Linux for Advanced Penetration Testing - Third Edition [Book]](https://www.oreilly.com/api/v2/epubs/9781789340563/files/assets/54634bb5-301a-4657-87ae-7833d4631248.png)